Data to enrich your trades business
Introducing JMServices Job System Pro - the ultimate, AI-powered, cloud-based job management solution. Manage jobs, customers, suppliers, and inventory in one place. Use our exclusive JMSGlobr™ Jobs Map to manage staff and view nearby jobs on-the-go. Go digital and streamline your management process with JMServices.
Everything you need to streamline your workflow.
Every tool available at the tip of your fingers, your all-in-one company dashboard.
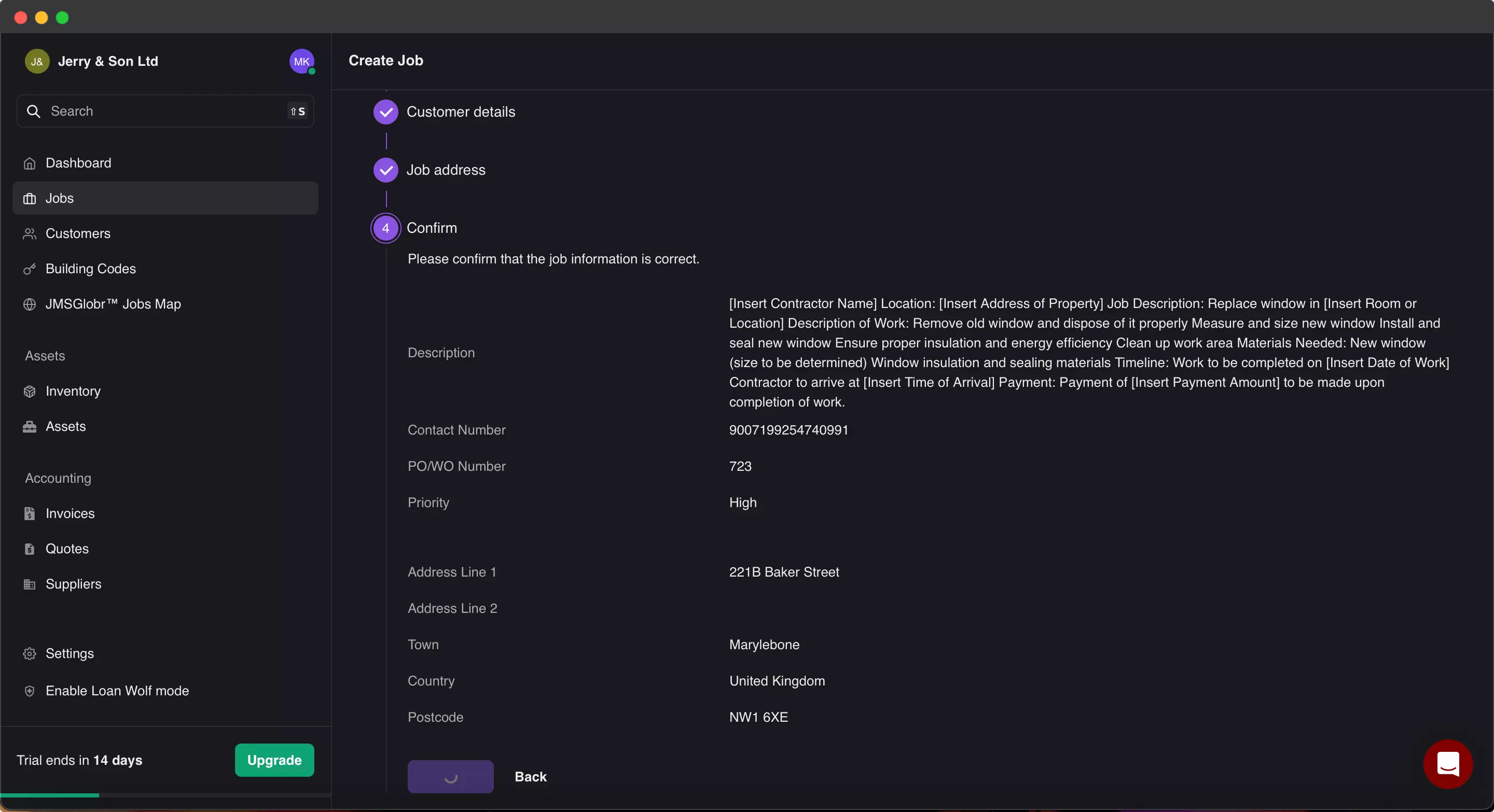
Efficiently manage all your jobs with features like time tracking, inventory management, job actions, and much more.
Oh wait, theres more?
Absolutely! We've included even more features to make this the ultimate workforce management solution. Designed by traders, for traders - this tool is exactly what you need.
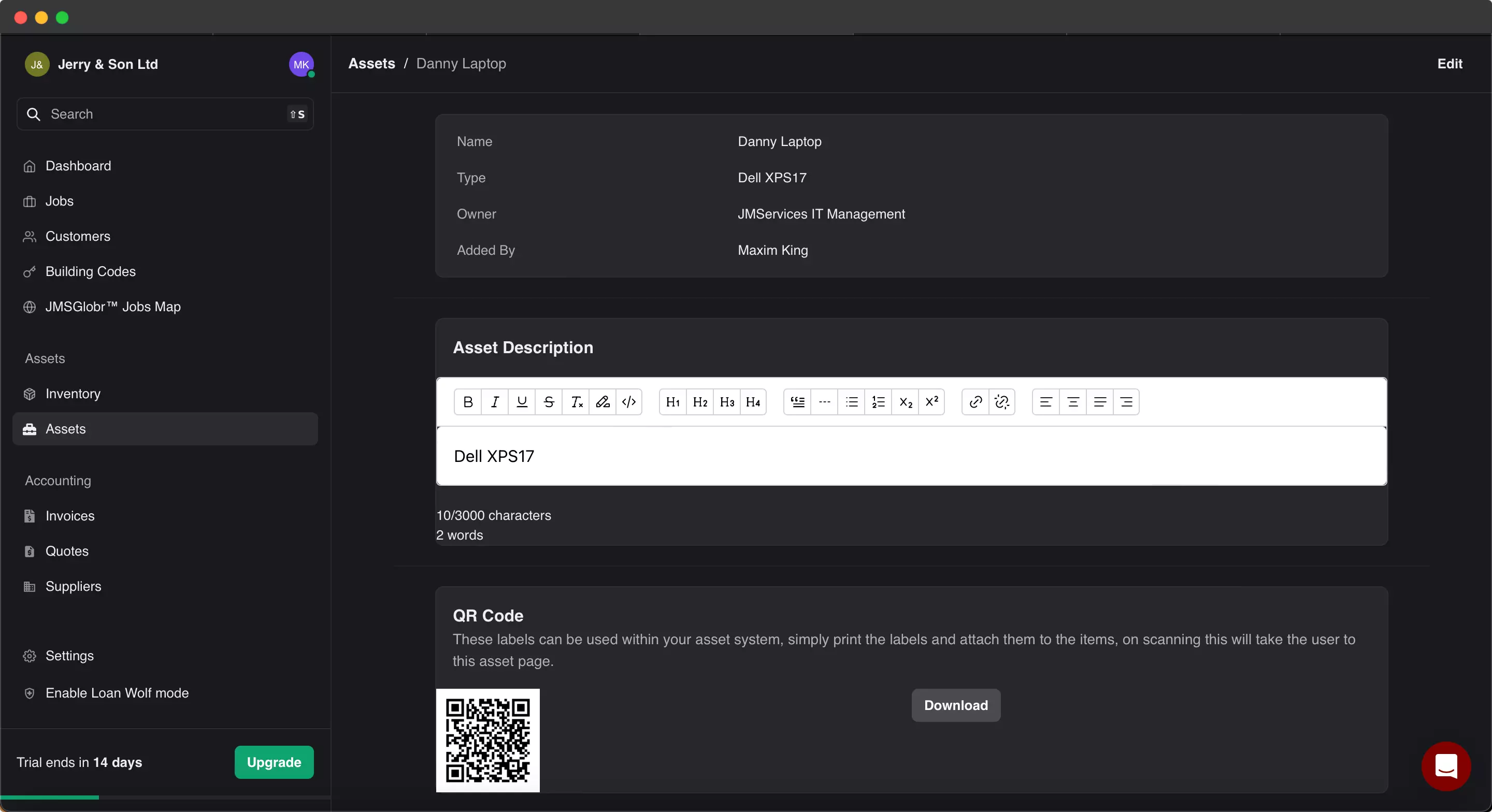
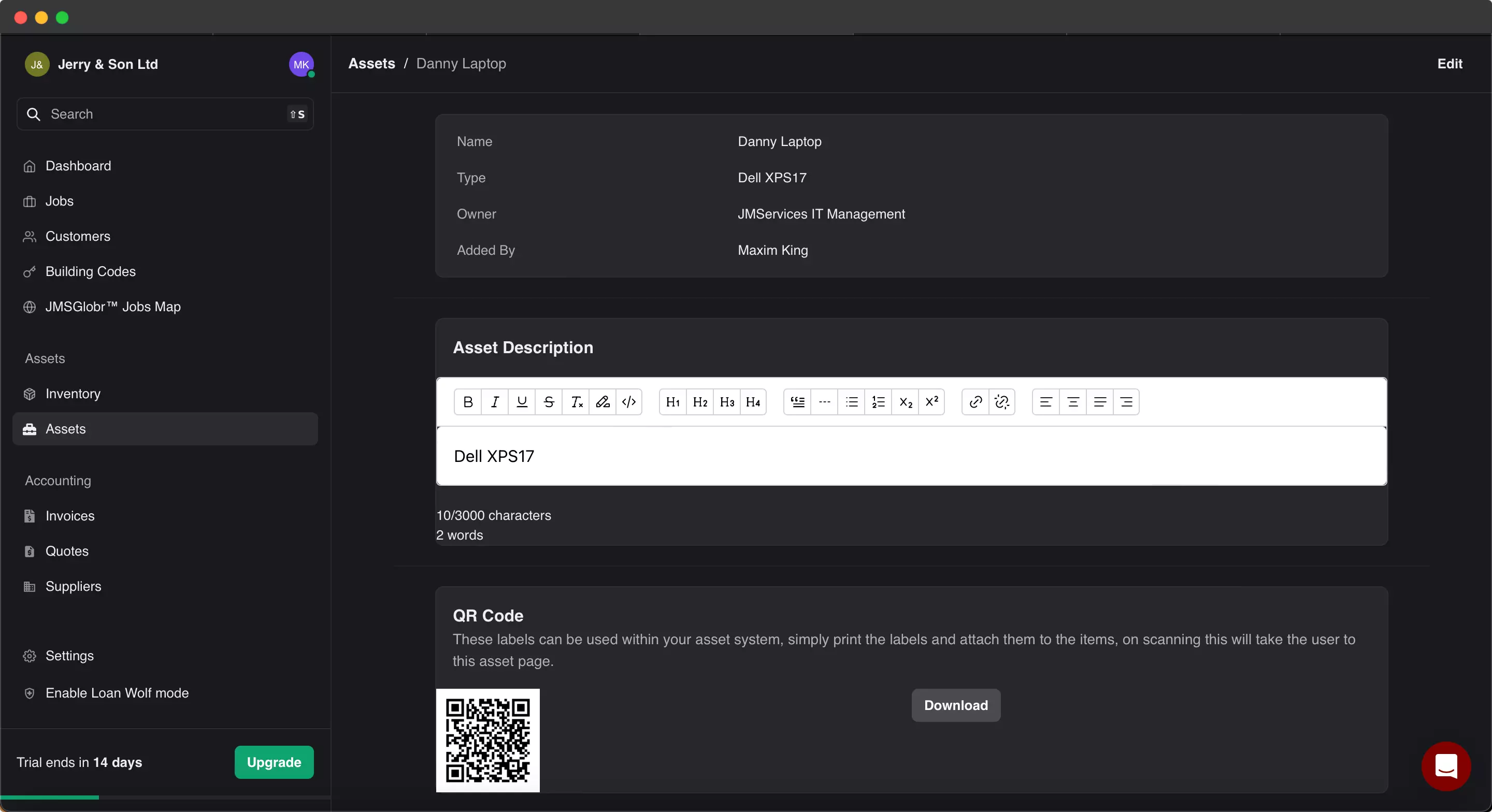
Assets management
Keep track of company assets using our assets management module.
Our integrated asset management system allows you to monitor all of your company's assets efficiently. With the system's barcode generation feature, your staff can easily locate and track products by simply scanning them.
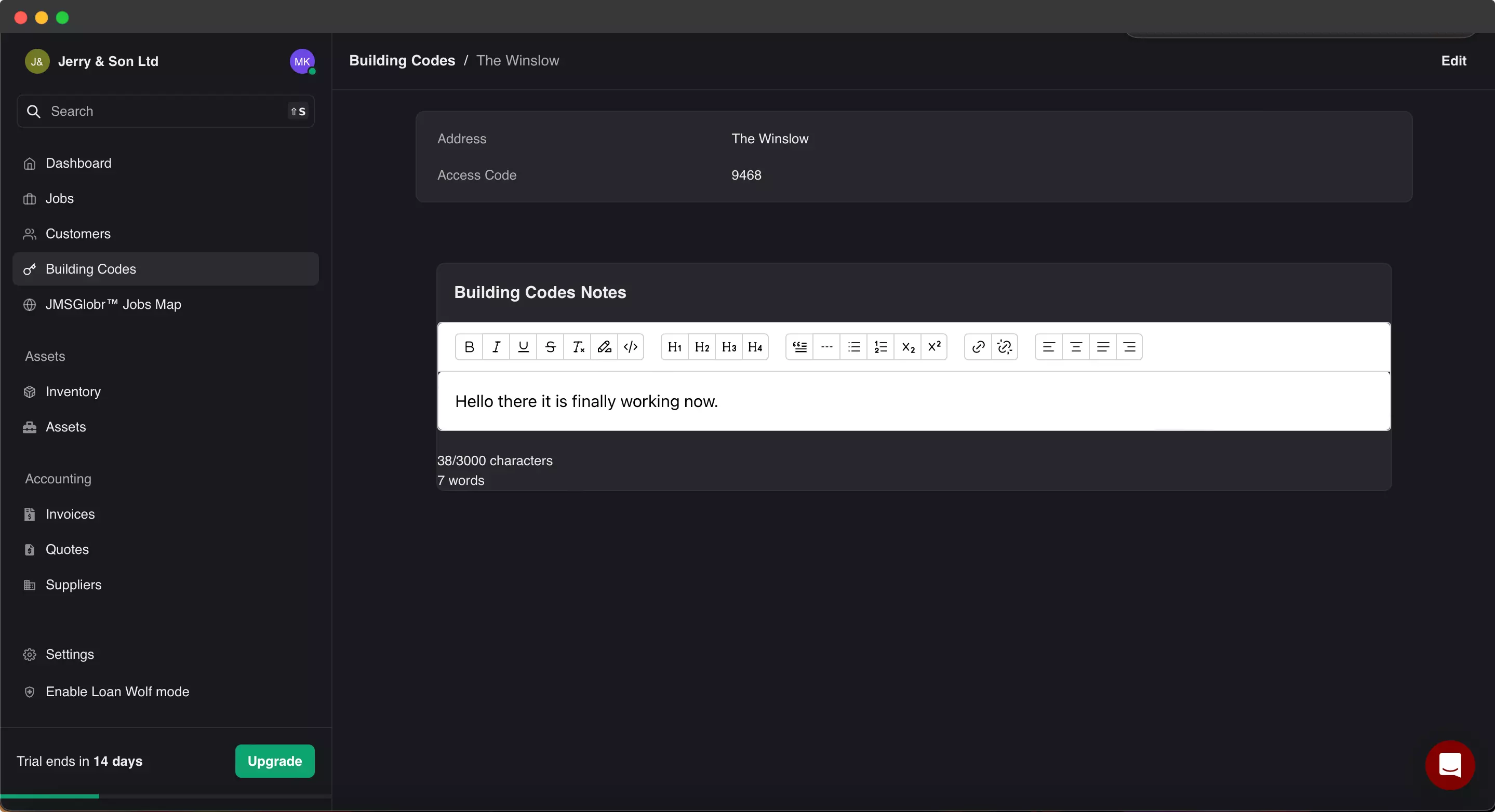
Building management
Building management made easy via our simple sites solution.
Effortlessly handle building codes and grant your staff instant access to buildings with just a click of a button. You can assign codes to specific jobs and customers for seamless tracking and management.
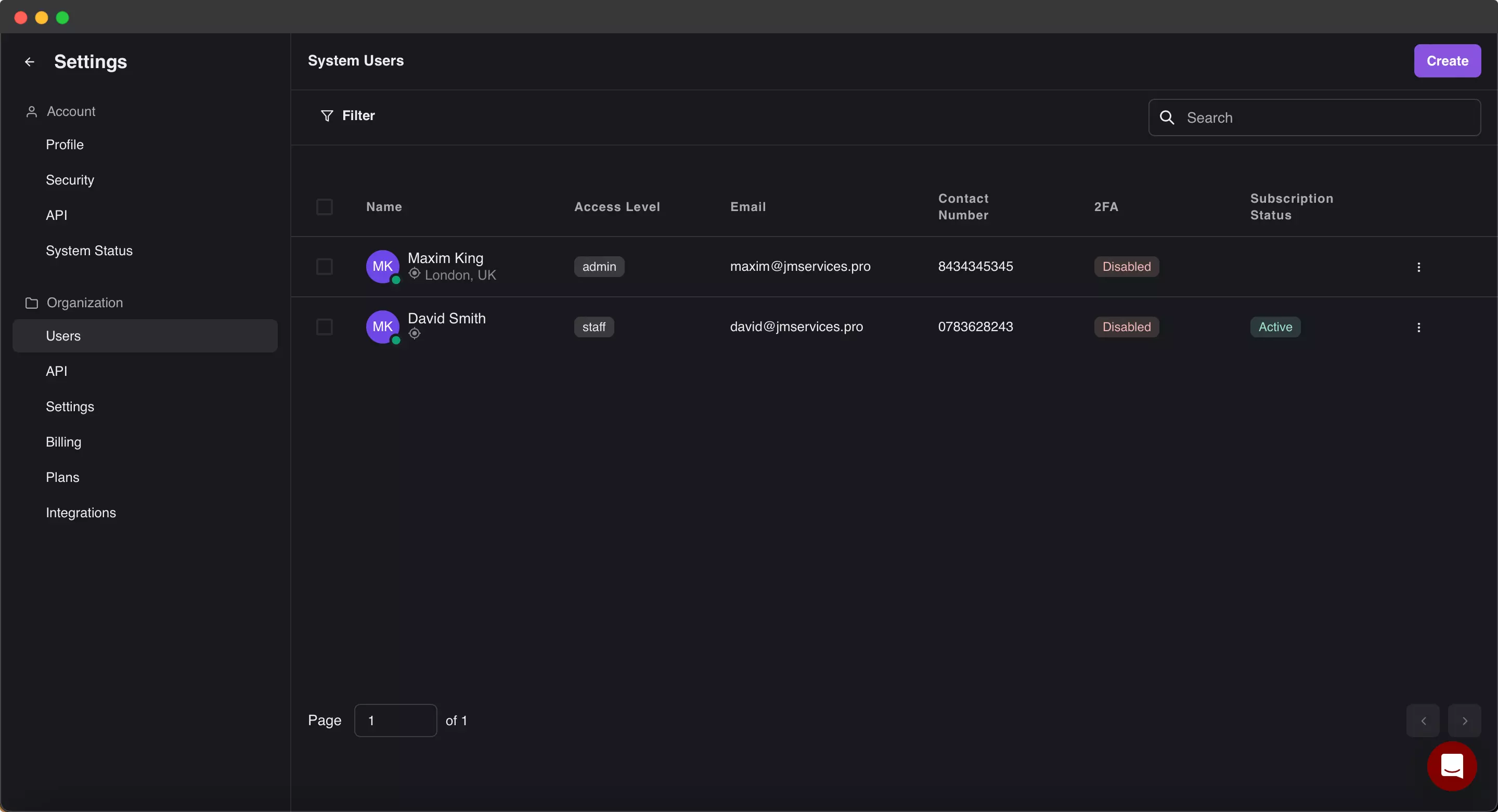
Staff management
Manage all your operators.
Efficiently manage your operators and contractors by assigning access levels and creating new staff accounts through your admin dashboard. Stay in control of your workforce and streamline the management process.
Keep track of company assets using our assets management module.
Our integrated asset management system allows you to monitor all of your company's assets efficiently. With the system's barcode generation feature, your staff can easily locate and track products by simply scanning them.
Building management made easy via our simple sites solution.
Effortlessly handle building codes and grant your staff instant access to buildings with just a click of a button. You can assign codes to specific jobs and customers for seamless tracking and management.
Manage all your operators.
Efficiently manage your operators and contractors by assigning access levels and creating new staff accounts through your admin dashboard. Stay in control of your workforce and streamline the management process.
Everything you need
Goodbye, spreadsheets!
JMServices is steadfast in our resolve to transition away from paper job sheets and manual spreadsheets. Consequently, we've architected an all-encompassing platform, consolidating essential tools to streamline operations and foster digital efficiency.
- 2FA/MFA Protection
- Fortify your JMServices account against unauthorized access with our Multi-Factor Authentication (MFA) mechanism. Activating MFA introduces an augmented security layer, mandating a distinct verification code in conjunction with your password.
- Invoicing Integrations
- Effortlessly manage and monitor your financial transactions with our Invoicing Integrations. Leveraging the power of QuickBooks, our integration allows seamless assignment of jobs to invoices within the app, streamlining your billing process and ensuring accuracy.
- State-of-the-art Security
- Security is intrinsic to JMServices' operational ethos. Our specialized team harnesses sophisticated protocols and measures, ensuring proactive identification and mitigation of potential risks. Leveraging continuous monitoring and state-of-the-art encryption, we guarantee the integrity and safety of your business data at all junctures.
- Streamlined Staff Management
- JMServices has meticulously crafted a sophisticated staff management system to seamlessly harmonize team workflows. Built upon strategic insights, this platform adeptly aligns organizational structures and roles, ensuring every team member operates at peak productivity. Our commitment remains unwavering: to elevate collaboration and drive superior organizational outcomes.
- Daily Backups
- JMServices underscores its dedication to data integrity through a meticulously architected backup strategy distributed across key UK locations. This systematic approach not only mitigates vulnerabilities but is emblematic of our unwavering commitment to paramount data security. In any unforeseen eventuality, rest assured our stringent Recovery Time Objective (RTO) will facilitate prompt and accurate data restoration.
- Privacy focused
- At JMServices, privacy is paramount in our operational blueprint. Our infrastructure is fundamentally architected around data confidentiality, housing all analytics, databases, and APIs internally. This guarantees your data's containment within our servers, providing unparalleled safeguarding of your sensitive information.
Simple pricing, no commitment
From startups to established enterprises, our diverse plans cater to all. Explore our pricing tiers to discover the ideal solution tailored for your team's needs.
Standard
£20
GBP
Billed monthly / per user
- Job management
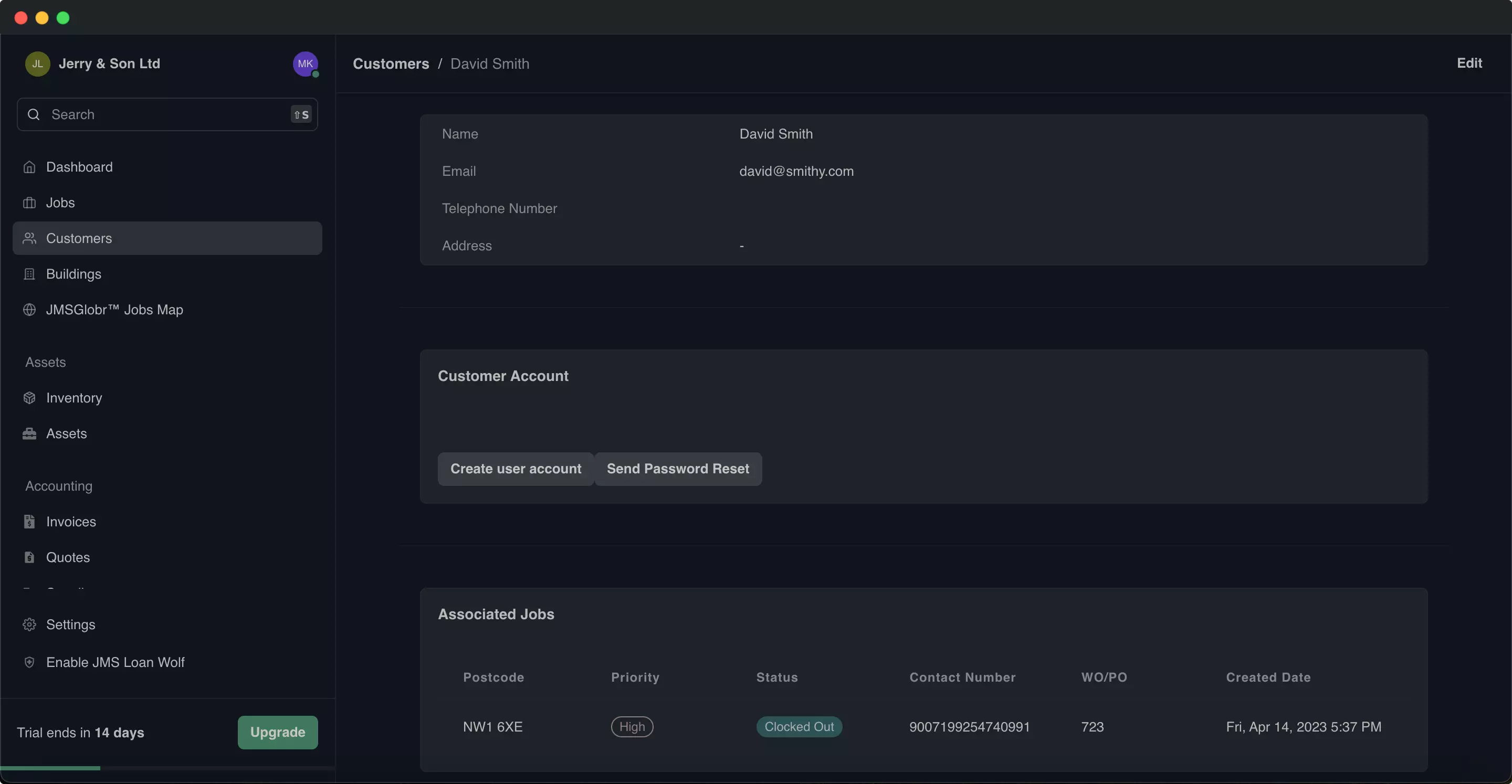
- Customer management
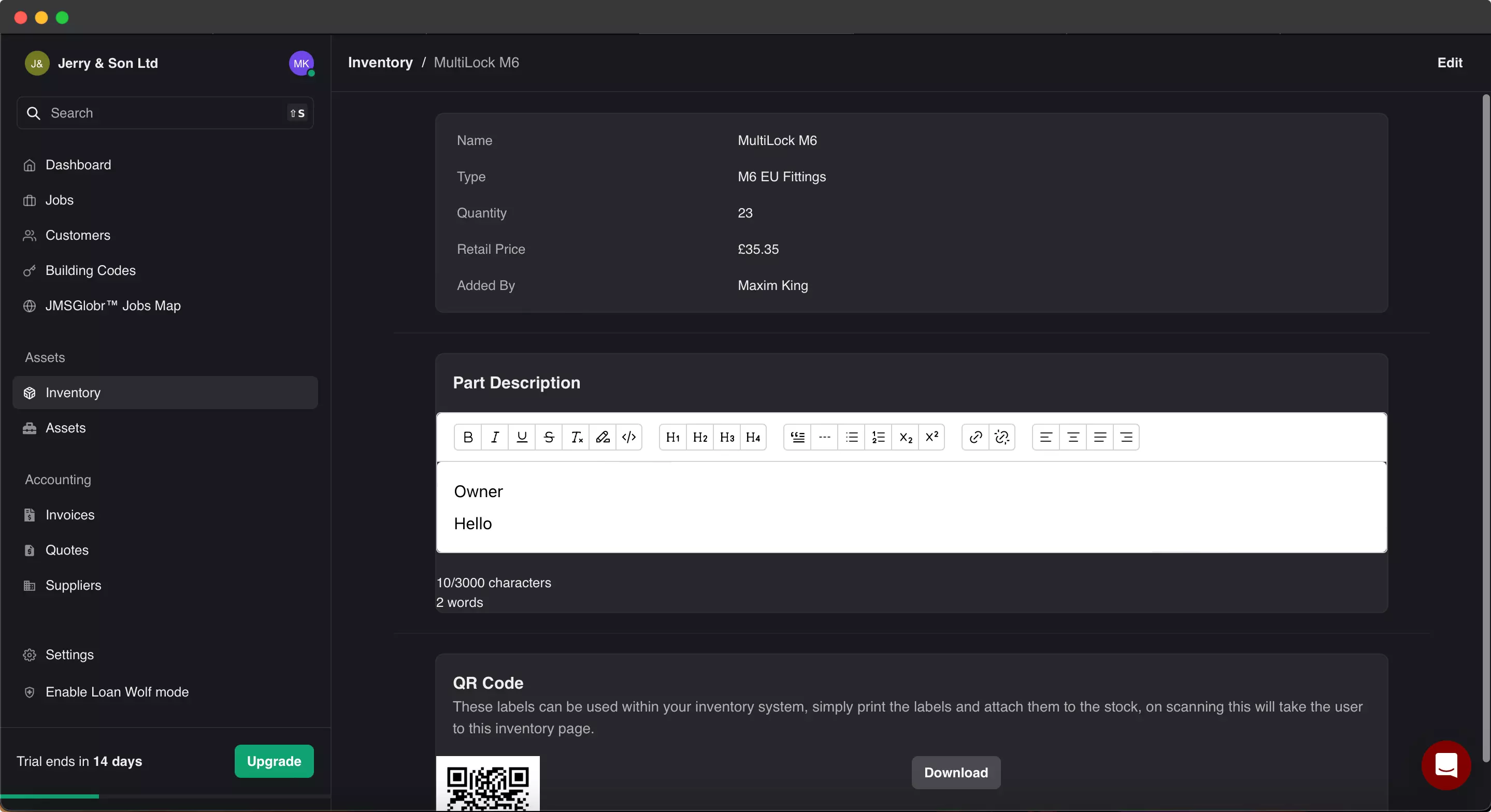
- Inventory & Stock Control
- Building codes management
- 1 additional user included
Premium
£30
GBP
Billed monthly / per user
- All Standard Features
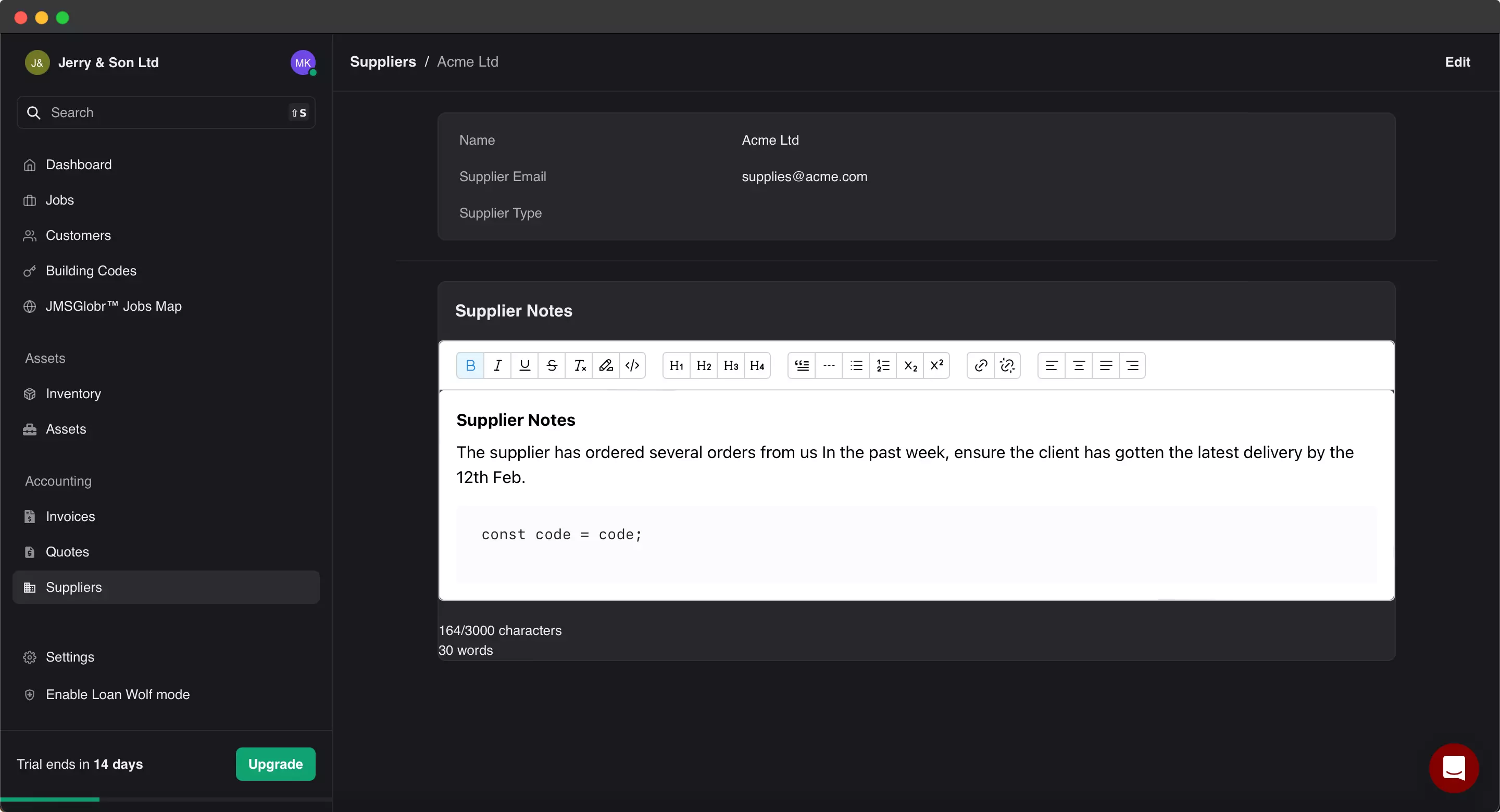
- Suppliers management
- Custom domain management
- Unlimited Quotes & Invoices
- Dedicated EU Instance
- 2 additional users included
- AI Powered Assistant
Enterprise
POA
GBP
Billed monthly / per user
- All Premium Features
- Dedicated account manager
- Customer Portal
- Bulk supplier discounts
- Custom plugin development
Feature comparison
Standard
The Standard License: ideal for businesses in their early stages.
Centered around traders
- AI Powered Assistant
- No
- Job management
- Yes
- Customer management
- Yes
- Stock & Inventory management
- Yes
- Building Codes management
- Yes
- Assets management
- No
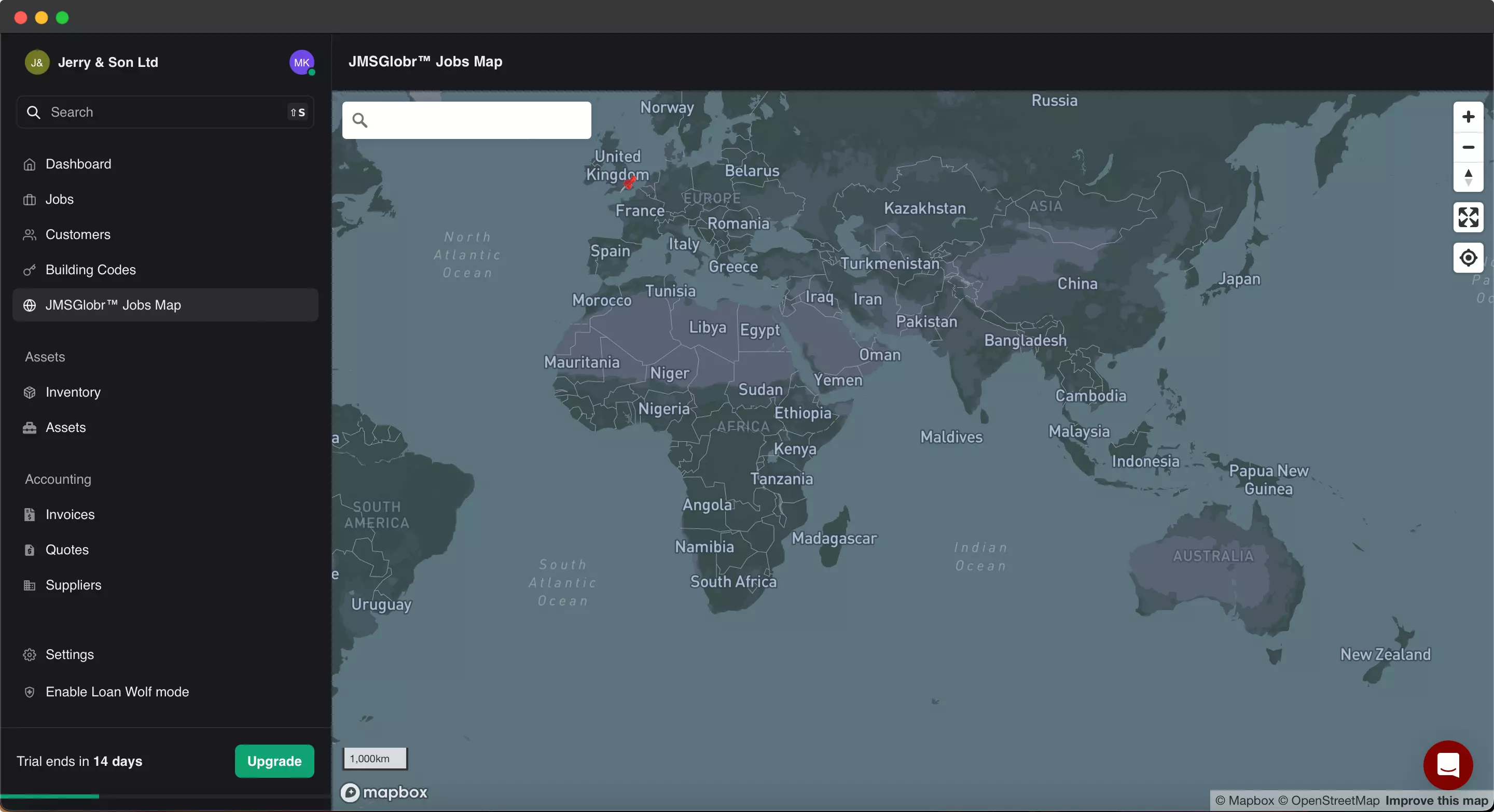
- JMSGlobr™ Mapping Solution
- Yes
- Supplier management
- No
- Xero & QuickBooks Integration
- No
- Additional users
- 1
All other features
- Mobile Operations
- iOS & Android
- Support
- Email, Live Chat
- Customer Portal
- No
- Dedicated account manager
- No
- Instant notifications
- Yes
- Bulk discounts
- 5+ users
- Custom Plugin Development
- $
Premium
The Premium License is designed for businesses that are ready to take the next step in their growth journey.
Centered around traders
- AI Powered Assistant
- Yes
- Job management
- Yes
- Customer management
- Yes
- Stock & Inventory management
- Yes
- Building Codes management
- Yes
- Assets management
- Yes
- JMSGlobr™ Mapping Solution
- Yes
- Supplier management
- Yes
- Xero & QuickBooks Integration
- Yes
- Additional users
- 2
All other features
- Mobile Operations
- iOS & Android
- Support
- Priority Email, Live Chat
- Customer Portal
- Yes
- Dedicated account manager
- Yes
- Instant notifications
- Yes
- Bulk discounts
- 5+ users
- Custom Plugin Development
- $
Enterprise
The Enterprise License is tailored for larger commercial applications that require advanced features and customization options.
Centered around traders
- AI Powered Assistant
- Yes
- Job management
- Yes
- Customer management
- Yes
- Stock & Inventory management
- Yes
- Building Codes management
- Yes
- Assets management
- Yes
- JMSGlobr™ Mapping Solution
- Yes
- Supplier management
- Yes
- Xero & QuickBooks Integration
- Yes
- Additional users
- Bulk Licences
All other features
- Mobile Operations
- Custom Application (iOS & Android)
- Support
- Priority Email, Live Chat & Phone
- Customer Portal
- Coming Soon
- Dedicated account manager
- Yes
- Instant notifications
- Yes
- Bulk discounts
- Yes
- Custom Plugin Development
- Yes
Feature comparison
Centered around traders
| Feature | Standard tier | Premium tier | Enterprise tier |
|---|---|---|---|
| AI Powered Assistant | No | Yes | Yes |
| Job management | Yes | Yes | Yes |
| Customer management | Yes | Yes | Yes |
| Stock & Inventory management | Yes | Yes | Yes |
| Building Codes management | Yes | Yes | Yes |
| Assets management | No | Yes | Yes |
| JMSGlobr™ Mapping Solution | Yes | Yes | Yes |
| Supplier management | No | Yes | Yes |
| Xero & QuickBooks Integration | No | Yes | Yes |
| Additional users | 1 | 2 | Bulk Licences |
All other features
| Feature | Standard tier | Premium tier | Enterprise tier |
|---|---|---|---|
| Mobile Operations | iOS & Android | iOS & Android | Custom Application (iOS & Android) |
| Support | Email, Live Chat | Priority Email, Live Chat | Priority Email, Live Chat & Phone |
| Customer Portal | No | Yes | Coming Soon |
| Dedicated account manager | No | Yes | Yes |
| Instant notifications | Yes | Yes | Yes |
| Bulk discounts | 5+ users | 5+ users | Yes |
| Custom Plugin Development | $ | $ | Yes |